
-
<Elliptic> North Korea's crypto hackers have stolen over $2 billion in 2025Analysis (2025)
<TRM> 2025-12-18, North Korea and the Industrialization of Cryptocurrency Theft
<US Department of Treasury> 2025-7-24, Treasury Sanctions Clandestine IT Worker Network Funding the DPRK’s Weapons Programs.
<Chainalysis> 2025-10-1, DPRK IT Workers: Inside North Korea’s Crypto Laundering Network
<US Justice Department> 2025-1-23, Two North Korean Nationals and Three Facilitators Indicted for Multi-Year Fraudulent Remote Information Technology Worker Scheme that Generated Revenue for the Democratic People’s Republic of Korea (IT Worker)
<US Justice Department> 2024-12-12, Fourteen North Korean Nationals Indicted for Carrying Out Multi-Year Fraudulent Information Technology Worker Scheme and Related Extortions (IT Worker)
<UK, Office of Financial Sanctions Implementation> 2024-9-12, Advisory on North Korean IT Workers.
<38 North> 2024-8-21, North Korea’s International Network for Artificial Intelligence Research.
<US Justice Department> 2024-8-8, Justice Department Disrupts North Korean Remote IT Worker Fraud Schemes Through Charges and Arrest of Nashville Facilitator (IT Worker)
<KnowBe4 (cyber security company)> 2024-06-23, How a North Korean Fake IT Worker Tried to Infiltrate Us.
-
<U.S. Departments of State and Treasury, and the Federal Bureau of Investigation> 2022-5-16, GUIDANCE ON THE DEMOCRATIC PEOPLE’S REPUBLIC OF KOREA INFORMATION TECHNOLOGY WORKERS.
-
<UN Security Council Arri-formula> 2025-1-14, Security Council Arria-formula on "Commercial Spyware and the Maintenance of International Peace and Security".
DPRK Cyber Actor and IT worker ties to UN Designated Entities
(Source: MSMT)
Nearly all DPRK cyber units and overseas IT workers identified in this report operate under or in support of UN-designated DPRK entities, including the Reconnaissance General Bureau, Ministry of National Defense, Ministry of Atomic Energy Industry, and the Munitions Industry Department, as well as the Korean Workers’ Party, which is subject to an assets freeze.
DPRK cyber actors and IT workers deployed abroad typically function through front companies that publicly represent these state entities. These front companies facilitate sanctions-violating activities—such as IT services, procurement, and money laundering—on behalf of UN-designated DPRK entities, activities that UN Member States are obligated to prevent.
Organization and Units Overview
April 13, 2026
Trending Video on X
In connection with the previous report, DPRK Monitor is highlighting a viral video related to recent developments. While its authenticity cannot be independently verified, the footage is garnering significant attention.
The video reportedly shows a U.S. corporate job interview where the candidate is asked to insult Kim Jong Un. The interviewee appears to have frozen up in response to the demand.
April 11, 2026
The Loyalty Trap: "Kim Jong Un Test" Used to Identify DPRK IT Infiltrators
According to an distinguished expert of North Korea, Mr. Gomi Yoji (五味 洋治), North Korean IT operatives are utilizing sophisticated AI and deepfake technology to infiltrate Western companies as remote software engineers. Operating under the direction of the Reconnaissance General Bureau (notably "Unit 121"), these individuals bypass recruitment filters using stolen identities—including the specific alias "Osamu Odaka"—and digital face-swapping during interviews.
A unique psychological "litmus test" has emerged in the recruitment process, where interviewers ask applicants to criticize or insult Kim Jong Un. This tactic banks on the operatives' deep-seated indoctrination and state-mandated refusal to disparage the Supreme Leader. However, while this "modern-day fumie" (stepping stone test) highlights the rigid loyalty of these workers, experts warn it is not foolproof as agents may be trained to perform or adapt to these specific lines of questioning to maintain their cover.
The primary objectives of these operations remain the generation of significant illicit revenue—estimated at millions of dollars—to fund the DPRK's nuclear programs, alongside the theft of sensitive corporate data for extortion.
Source: The Naigai Times
February 21, 2026
Analytical Brief: Profile of Sim Hyon-sop Based on Diplomatic Testimony
This report highlights the information provided by Ryu Hyun-woo (류현우), a former DPRK Ambassador to Kuwait, regarding the high-profile North Korean financial operative Sim Hyon-sop.
Please read below artciel "From Fake IT Jobs to Fiat Cash: Mapping the DPRK IT Worker Crypto Laundering Network (December 31, 2025)" as well.
Key Data Points and Findings
FBI Photographic Identification: Ryu Hyun-woo dismisses the first of the three FBI-released photos as inaccurate.
- The second and third photos are confirmed as authentic likenesses from that period, with the second (middle) photo cited as the most accurate representation of Sim.
Operational Role in the Middle East:
Following the 2017 tightening of international sanctions, North Korean laborers were forced to withdraw from the UAE and broader Gulf region.
Sim Hyon-sop was recruited by the DPRK embassy to manage the recovery of outstanding wages and facilitate complex remittances.
He was chosen for his fluency in languages, deep expertise in banking systems, and extensive local knowledge in Dubai.
Personal Profile and Conduct:
Physicality: Approximately 180cm tall with a stout/heavier build.
Temperament: Described as "tight-lipped" and taciturn; a personality highly favored by North Korean high-ranking officials.
Lifestyle: Despite managing massive sums of money, he lived modestly and never engaged in ostentatious spending.
Psychological State: He reportedly lived in a state of constant anxiety due to the perpetual use of aliases, though he was noted as a devoted father to his daughter.
Current Location:
- Intelligence from Ryu’s contacts suggests Sim has relocated to Dandong, China, where he is currently residing with his family.
Source: 채널A WORLD.
Park Jin Hyok
RGB Cyber Actor
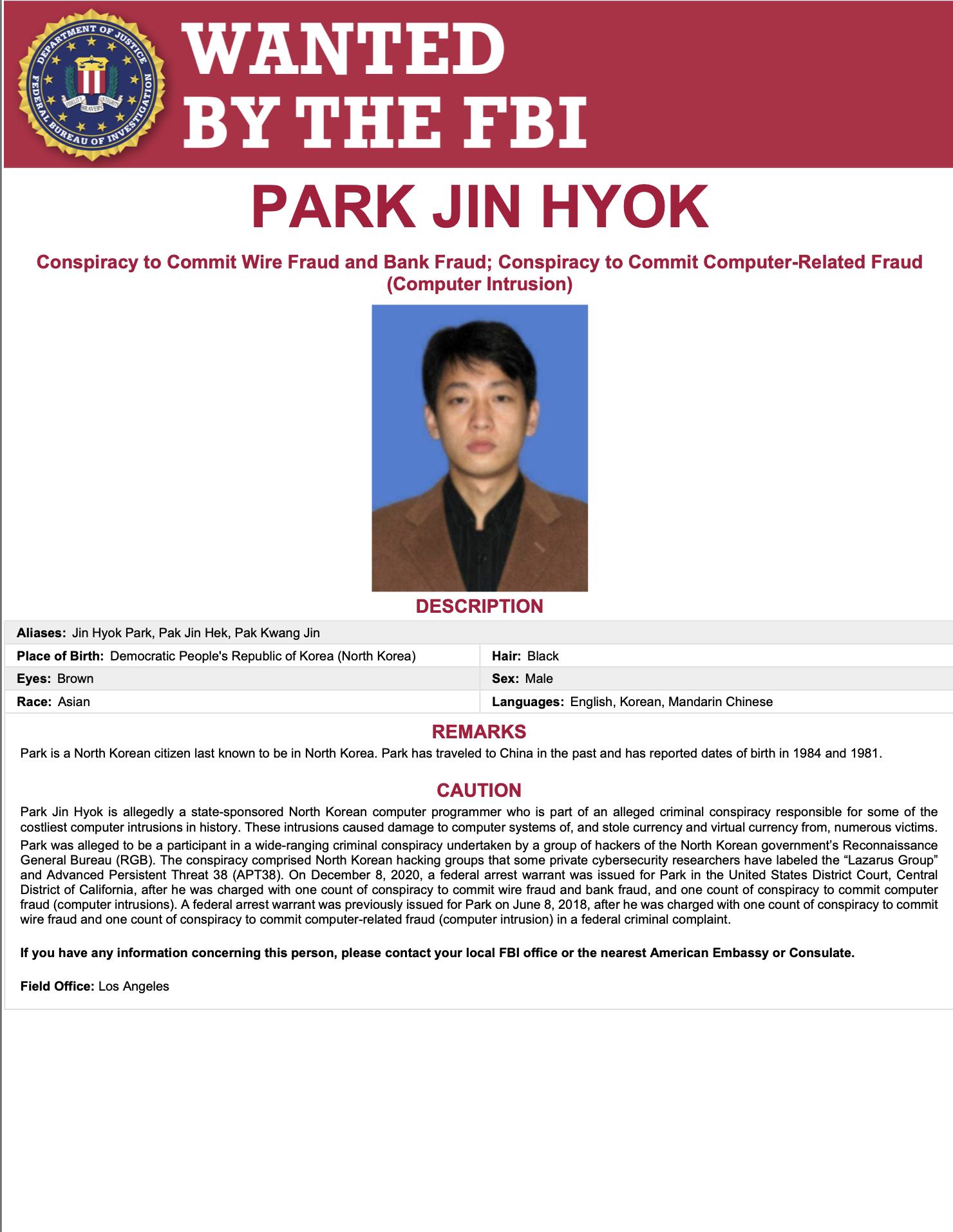
Source: FBI.
Park Jin Hyok is a US-indicted, state-sponsored North Korean programmer linked to the Reconnaissance General Bureau, accused of orchestrating large-scale cyber intrusions and theft of fiat and virtual currency as part of the Lazarus Group/APT38 network.
Arrest warrants and charges
June 8, 2018: U.S. federal arrest warrant issued for conspiracy to commit wire fraud and computer intrusion.
December 8, 2020: Superseding arrest warrant issued by the U.S. District Court (Central District of California), charging conspiracy to commit wire fraud, bank fraud, and computer fraud.
Multilateral Sanctions Monitoring Team (MSMT) 2nd Report Rollout Event
January 12, 2026
Following statements by MSMT member States, private sector entities (Google Threat Intelligence Group, Palo Alto Networks, Sekoia.io, and Upwork) briefed on the DPRK’s cyber activities and overseas IT worker schemes that violate UN Security Council resolutions.
They outlined key operational methods used by the DPRK, including cyber-enabled revenue generation, illicit employment arrangements, and identity obfuscation techniques.
In response to questions from the floor, the speakers further addressed the role of public–private partnerships, hiring and recruitment mechanisms, and the use of artificial intelligence in detecting and disrupting DPRK deception tactics, including the identification of fraudulent identities and covert IT worker networks.
<Summaries>
Google Threat Intelligence Group:“North Korea’s Crypto Heist Machine: From Social Engineering to Laundering”
North Korean threat actors have stolen at least $2 billion in cryptocurrency since January 2025, accounting for at least 60% of all cryptocurrency thefts worldwide last year.
Operations rely on a combination of social engineering, including email phishing, social media engagement, and IT workers applying for fraudulent employment under false pretenses.
Recent tactics involve compromising software providers and services used by cryptocurrency entities, such as wallet providers and IT services.
In the 1.5-billion-dollar Bybit heist, hackers compromised reserve account management software while tricking employees into approving transactions.
The regime uses blockchain-based laundering tactics, including swapping between different types of cryptocurrencies and using mixers to hide the origin of stolen funds.
Laundered cryptocurrency is converted into cash through a network of regime operatives and facilitators to support any of the regime's objectives.
Palo Alto Networks: “Getting a Job Is the Job: North Korea’s Industrialized Fake Hiring and Revenue Pipeline”
For the North Korean regime, getting a job is their job, with thousands of citizens specifically trained for various parts of job-hunting campaigns.
The system is a mechanized system honed over years of training to exploit how companies hire.
The regime utilizes "identity mules" in country who willingly sell out their own identity to facilitate these hires across all six inhabited continents.
Money that would have been fed back into local economies or paid as payroll taxes is instead remitted over to Pyongyang.
This system will not go away until there is better international cooperation and cooperation with private industry to make the system harder to take advantage of.
Sekoia.io: “Hunter–Killer Teams Inside the Enterprise: North Korea’s Insider-Enabled Cyber Model”
IT workers and attack units function as "Hunter Killer teams" (Hunter Killer teams), where IT workers act as an insider threat and perform reconnaissance for attack units.
Recommended the implementation of corporate intelligence systems similar to anti-money laundering mechanisms.
Companies must know their employees, identify disgruntled individuals, and rely upon unit cohesion.
Employers should use their imagination to move people away from remote only situations and look at them face to face.
Constant adaptation is necessary because these actors are adapting their TTPs relentlessly.
Upwork: “From Wigs to Weaponized Identity: North Korea’s Professionalized IT Worker Threat”
North Korean IT workers have evolved from a rudimentary group using masks and wigs to a highly sophisticated, well-funded, and well-organized nation-state.
The fundamental issue is "identity" and whether it can be moved physically or virtually.
Facilitators are now able to bypass rigorous background checks and controls established by government advisories.
In some cases, individuals hired for office-based roles have allowed North Korean IT workers remote access to the network to perform their work overnight.
Job applicants are no longer competing against people with similar skills, but against professional facilitators whose sole role is to gain the job.
2 Response to Questions (by Speaker)
1. Public-Private Partnerships
Google Threat Intelligence Collaboration with the public sector is a mechanism for raising awareness and combating malicious activities. Operating unique digital infrastructure provides insights that allow for the design of specific protections when certain types of companies are targeted. Sharing information between sectors changes the game in combating North Korean cyber operations.
Sekoia.io Private sector collaboration functions like iron sharpening iron, where identifying bad actors and mapping out command and control infrastructure benefits all peers. Success is defined by interrupting an attack before it is detonated by sharing live, fresh artifacts.
Palo Alto Networks Developing the muscle for investigating incidents and making HR systems resilient is a result of concentrated work on this threat. Support is available to help the private sector become resilient free of charge. Establishing trust with governments is essential so that information sharing does not jeopardize victims but imposes costs on attackers. This open-ended, high-trust sharing should be replicated internationally between countries.
Upwork Relationships with government partners serve as a great barometer of how everyone is upping their game. Regular information sharing helps level-set whether internal processes and controls are on par with industry standards. From a policy level, a safe harbor for industry sharing is critical to allow information to flow without fear of adverse impacts from sanctions.
2. Hiring Mechanisms
Palo Alto Networks Making systematic changes from a government perspective is difficult because it may disrupt business. Working with technically versed experts to lower the threshold for threats entering systems is a better approach. Referral-based hiring and establishing actual relationships with candidates will likely make a comeback. ID verification is the number one piece of protection; validating that the person interviewed is the same person starting work with a legitimate government ID goes a long way.
Upwork Establishing a safe harbor for industry information sharing at the policy level is critical. Since the hiring process often spans multiple companies and platforms, having the ability to share data across the industry is a necessary move forward.
Sekoia.io Embrace inconvenience by mixing up hiring practices. This strategy ensures the organization remains a difficult target to fix for threat actors.
3. Use of AI
Palo Alto Networks Deep fake technology is incredibly accessible, but it remains detectable through machine learning based algorithms that look at pixels and formulation. This detection technology is comparatively low-cost and can be implemented directly into the hiring process to flag suspicious signals. It is also logical to deploy this software for any employee authorized to transfer money to prevent financial crime involving impersonation.
Google Threat Intelligence Group From a security research perspective, suspicious artifacts can be pushed back through generative AI models to assess if an image, resume, or document was modified or created by AI. This provides a low barrier to entry for investigating a large volume of activity at scale. In many cases, models are capable of detecting if they or other models were used to generate a document.
(Edited by DPRK Monitor)
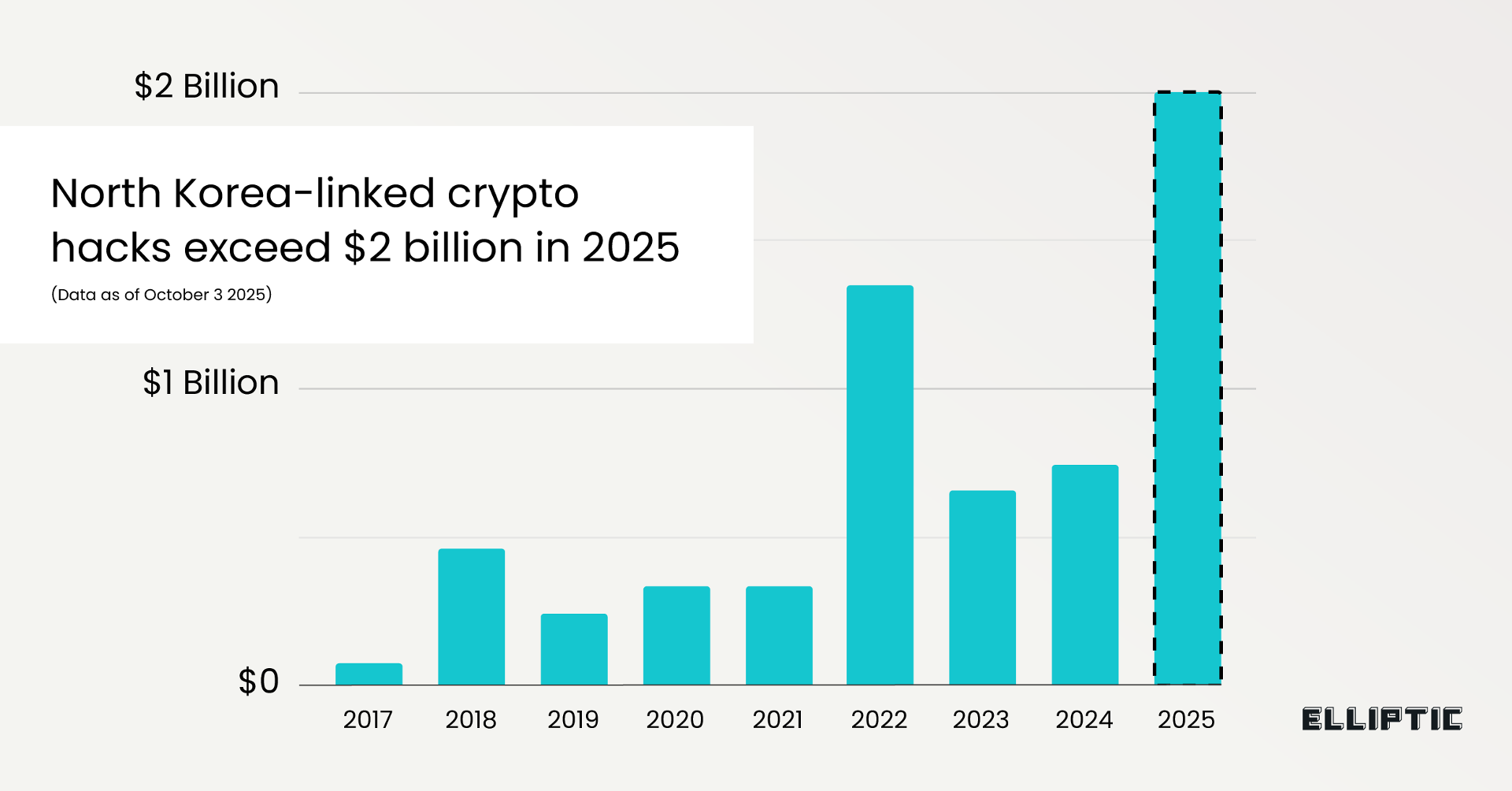
<Elliptic> DPRK Surpasses $2 Billion in Crypto Theft in 2025, Led by the $1.46B Bybit Hack and Advanced Laundering Tactics
January 6, 2026 (*The article was published by Elliptic on October 7, 2025)
<Summary>
Elliptic reports that DPRK-linked hackers have already stolen over $2 billion in cryptocurrency in 2025.
This figure includes more than thirty additional hacks attributed to the DPRK, notably incorporating the February 2025 $1.46 billion theft from Bybit, demonstrating a sustained operational tempo rather than isolated incidents despite increased global awareness and defensive measures.
A growing share of victims now includes high-net-worth individuals, reflecting a strategic pivot toward personally targeted theft rather than exclusively exploiting exchanges or on-chain protocols.
The campaign shows a clear rise in social engineering attacks, marking a shift from earlier attacks where technical flaws in smart contracts or infrastructure were the primary attack vectors.
Post-theft laundering strategies have become increasingly sophisticated and layered, involving repeated mixing, cross-chain transfers, obscure blockchains, and the exploitation of “refund addresses” to redirect assets to fresh wallets, reducing traceability and investigative visibility.
December 31, 2025 (*The article was published by Chainalysis on October 1, 2025)
<Chainalysis>From Fake IT Jobs to Fiat Cash: Mapping the DPRK IT Worker Crypto Laundering Network
DPRK IT workers generate cryptocurrency revenue by infiltrating global IT jobs, often being paid in stablecoins that are attractive to OTC traders as an off-ramp to fiat, with funds ultimately financing North Korea’s weapons programs.
Sanctions and enforcement actions target key facilitators, including the OFAC-designated Sim Hyon Sop (a Korea Kwangson Banking Corp rep who received tens of millions in DPRK IT worker crypto) and Lu Huaying, a Chinese OTC trader based in the UAE sanctioned for laundering DPRK IT worker proceeds.
DPRK IT workers are deployed via front companies such as Chinyong Information Technology Cooperation Company, sanctioned by OFAC and the Republic of Korea for employing DPRK IT labor overseas, and they use obfuscation techniques (VPNs, fake IDs) to conceal their identities.
After receiving stablecoin payments, DPRK IT worker funds are laundered through methods like chain-hopping, token swaps, and mixing, then consolidated and moved through intermediaries—including accounts tied to Kim Sang Man, a DPRK national and representative of Chinyong Information Technology Cooperation Company, Sim Hyon Sop, and OTC facilitator Lu Huaying—before conversion to fiat.
Read the full report in Japanese (北朝鮮IT労働者による暗号資産マネーロンダリングネットワークの内幕)

Who is Sim Hyon Sop?
Sim Hyon-Sop has allegedly played a central role in North Korea’s counterfeit cigarette trade since at least 2009, using front companies, false shipping records, and bulk cash payments to evade US sanctions.
Between 2021 and 2023, he and co-conspirators imported tobacco into the DPRK and laundered US dollar payments, with proceeds benefiting the regime’s WMD programs.
Us authorities charged Sim with conspiracy to violate the IEEPA, bank fraud, and money laundering, issuing an arrest warrant in 2023 and indictments in 2025.
On July 24, 2025, the U.S. State Department is offering up to $7 million for information leading to his arrest or conviction; notably, on April 26, 2023, it had already announced a reward of up to $5 million for information related to his alleged sanctions evasion involving illicit tobacco trade and money laundering.
Source:
US DOJ Civil Forfeiture Complaint
April 26, 2023: Reward of up to USD 5 million
US State Dept offers rewards for info leading to arrests of 3 transnational criminals
FBI Wanted Poster (archived) SIM HYON-SOP - FBI
July 24, 2025: Reward increased to up to USD 7 million
December 18, 2025
<TRM> DPRK and the Industrialization of Crypto Theft: How a Single State Actor Dominated Global Hack Losses in 2025
Cryptocurrency theft has become industrialized
The DPRK has systematized crypto theft into a repeatable and organized operation, combining cyber units, overseas IT workers, and laundering intermediaries rather than relying on isolated hacks.North Korea linked to the majority of global crypto hack losses in 2025
In 2025, more than USD 2.7 billion was stolen in cryptocurrency hacks worldwide, and well over half of that total was linked to a single nation-state actor: North Korea, according to TRM Labs.Fewer incidents, larger returns
DPRK-linked operations increasingly focus on high-value compromises, allowing outsized returns from a smaller number of attacks rather than frequent low-impact exploits.Human and organizational access is central
TRM Labs highlights the DPRK’s reliance on people-and-platform compromise, including embedded IT workers, impersonation, and abuse of internal trust at crypto-related firms.“Chinese Laundromat” as the off-chain exit mechanism
Stolen funds ultimately move into a Chinese-language laundering ecosystem, where intermediaries coordinate via WeChat and conduct off-chain settlement into Chinese yuan (CNY) or goods, marking the point at which assets leave the blockchain.
Source: DPRK Monitor.
December 18, 2025
<Chainalysis>2025 Crypto Theft Trends: DPRK Sets New Records With Fewer Attacks
North Korean hackers stole $2.02 billion in cryptocurrency in 2025, a 51% year-over-year increase, pushing their all-time total to $6.75 billion despite fewer attacks.
The DPRK is achieving larger thefts with fewer incidents, often by embedding IT workers inside crypto services or using sophisticated impersonation tactics targeting executives.
The DPRK shows clear preferences for Chinese-language money laundering services, bridge services, and mixing protocols, with a 45-day laundering cycle following major thefts.
Individual wallet compromises surged to 158,000 incidents affecting 80,000 unique victims in 2025, though total value stolen ($713M) decreased from 2024.
Despite increased Total Value Locked in DeFi, hack losses remained suppressed in 2024-2025, suggesting improved security practices are making a meaningful difference.
Read the full report in Japanese (北朝鮮による暗号資産窃取、年間で過去最高の20億ドルに)
August 8, 2025
Old Game, New Name: Sobaeksu and DPRK’s WMD Legacy
The US government has recently designated the Korea Sobaeksu Trading Company (Sobaeksu) for asset freezing, citing its involvement in foreign currency-generating activities conducted by DPRK IT workers.
However, by examining past DPRK Panel reports, it becomes clear that Sobaeksu is in fact connected to companies previously involved in WMD development—namely, NAMCHONGANG TRADING CORPORATION (NCG) and KOREA MINING DEVELOPMENT TRADING CORPORATION (KOMID).
Sobaeksu
朝鲜小白水联合会社
Namchonggang
KOMID
Yun Ho-Jin
Source: DPRK NM Inventory Safeguards Agreement - 4 May 1992 by IAEA Imagebank by Flicker (Edited by DPRK Monitor).NCG was previously engaged in North Korea’s nuclear development, particularly in procurement related to uranium enrichment, while KOMID was involved in missile transactions. These DPRK entities linked to the development and sale of WMDs have continued their operations under different names.
UNSCR 2270 (2016) pointed out that NCG had changed its name to Namhung Trading Corporation (Namhung).
A review of corporate information registered in China shows that Namhung and the Beijing office of Sobaeksu shared the same address.
The representative of Sobaeksu’s Beijing office is Yun Ho-Jin, who was formerly the head of NCG. Yun Ho-Jin (윤호진 in Korean, 尹浩真 in Chinese) is listed under UN sanctions and is a former DPRK diplomat who was involved in uranium enrichment-related procurement at least as far back as the 1990s. His name is currently registered as the representative of Sobaeksu’s Beijing office.
Kim Chol Nam (김철남 in Korean, 金哲南 in Chinese), listed as a director of Sobaeksu’s Dandong office, is also registered as the representative of Korea Changgwang Trading Corporation in Beijing. Past Panel investigations have confirmed that Korea Changgwang Trading Corp is an alias for KOMID.
August 3, 2025
Part of DPRK’s Hard Currency Network
While the US has imposed sanctions on DPRK’s activities in Southeast Asia, the UN Security Council DPRK Panel of Experts (POE) report—covering the newly sanctioned individuals Kim Se Un and Sobaeksu—offers key new information. DPRK Monitor shares additional context below.
DPRK individuals operate or control multiple registered entities in various countries and engage in several distinct areas—including IT, trading, finance, and, in some cases, money laundering, military logistics, or procurement. These individuals often obtain passports from host countries or assume foreign identities to travel across multiple jurisdictions—thereby enhancing both their mobility and concealment.
Kim Se Un
김 세 운
Date of Birth: 25 March 1978
Passport: Passport 390120007 (DPRK) issued 09 Jan 2020 expires 09 Jan 2025 (individual)

Source: US Department of State.According to the US State Department, Kim Se Un is a North Korean representative of Korean Sobaeksu Trading Company (Sobaeksu) and was involved in a scheme from April 2021 to June 2023 to smuggle tobacco into DPRK and pay in US dollars, violating US sanctions. The operation used false shipping records and bulk cash to evade restrictions.
From Vietnam to Cambodia — A Wider Web
In the past, Kim Se Un also registered company in Cambodia. According to the POE report (S/2023/171, paras.155-157), Kim was the director of the Cambodia-based company U.J Import Export Co., Ltd (struck off by Cambodian authorities in December 2019, Figure 1).
Cooperated with Ri Chol Nam
Moreover, the POE reported Kim cooperated with Ri Chol Nam (리철남) (Figure 2,3), who was involved in money laundering, brokering sales of weapons, diamonds, and gold, and other illicit financial activities linked to the DPRK. Ri also engaged in potential sales of military-related equipment, including bulletproof vests acquired from third countries for resale.
The Expanding DPRK Network: Who’s Next?
DPRK Monitor will update Kim Se Un’s network!
Figure 1
Source: Cambodian corporate registry (Edited by DPRK Monitor).Figure 2
Source: DPRK Monitor.Figure 3
Source: DPRK POE S/2023/171, annex 85.Source: Maltego Graph Visualization (annotated by DPRK Monitor).Use of AI by DPRK
DPRK IT workers may use AI-generated fake ID during job interviews. A report by cyber security company also indicate their use of real-time deepfake technology. The most effective detection method is passing a hand over the face, which disrupts facial landmark tracking. Other recommended techniques include:
Rapid head movements
Exaggerated facial expressions
Sudden lighting changes
Companies are advised to adopt layered detection strategies in coordination with their information security teams. Below is an example of DPRK tactics.

Source: KnowBe4. “The picture (right) is an AI-enhanced version of the person who we interviewed during the hiring process, where the applicant’s face was added over a completely different unrelated person’s “stock photography” picture (left) so they looked more professional with glasses and wearing formal work attire.”
Source: KnowBe4, “North Korean Fake Employees Are Everywhere! How to Protect Your Organization” (Annotated by DPRK Monitor)